Tag: hostroyale
-

StrongVPN
StrongVPN is a virtual private network (VPN) service provider. A VPN is a service that encrypts a device’s internet connection and routes it through a server in a location of the user’s choosing. This can be used to protect the user’s privacy and security online, as well as to access content that may be restricted…
-

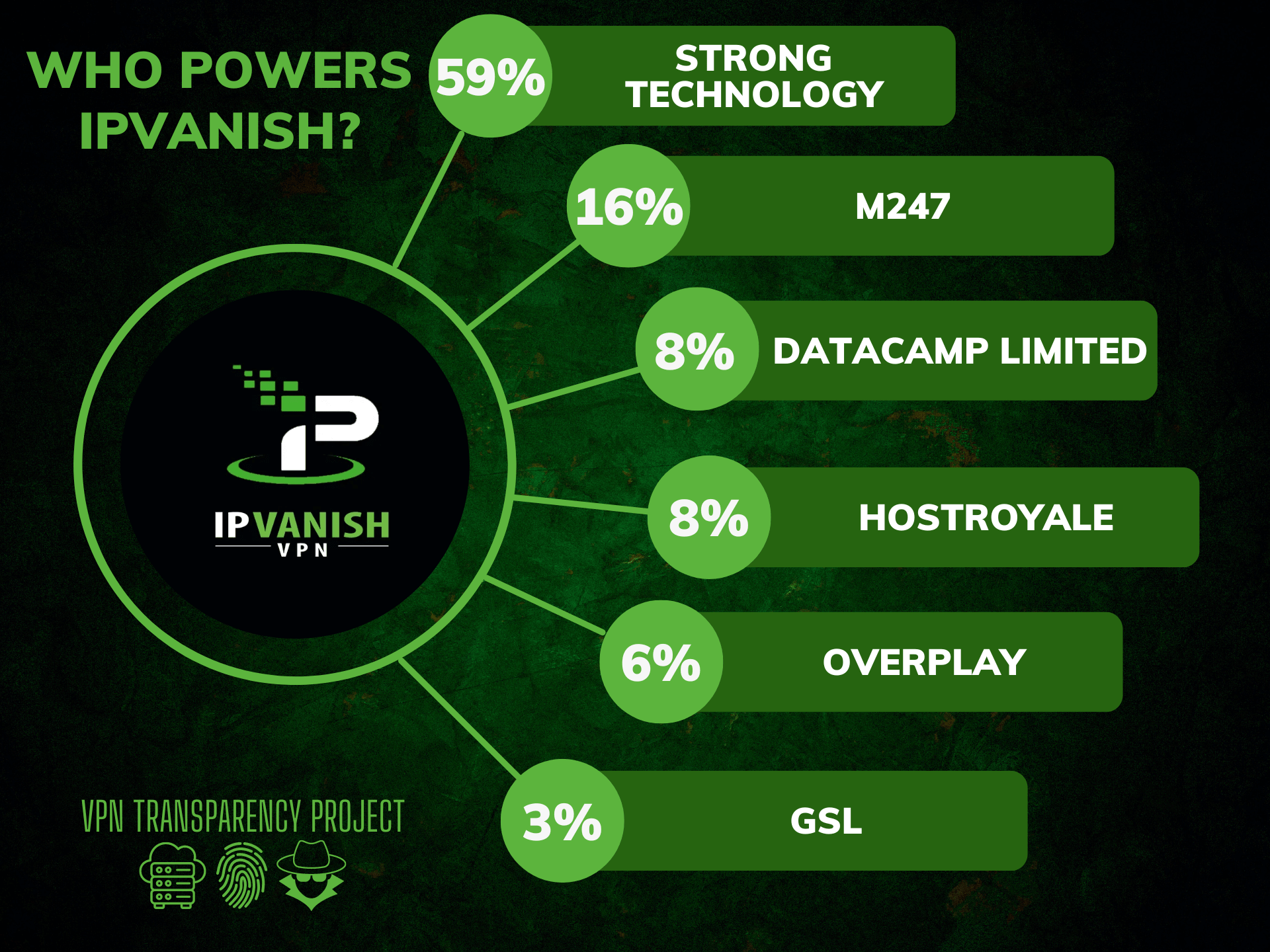
IPVanish
IPVanish is a virtual private network (VPN) service that allows users to securely and anonymously access the internet. A VPN creates a secure, encrypted connection between a device and the internet, protecting data and preventing snooping or tampering by third parties. IPVanish offers a range of VPN products and services, including support for Windows, Mac,…
-

Surfshark
Surfshark VPN is one of the most popular VPN services in 2022. Its competitive price and unlimited simultaneous connections make it a very attractive VPN option for all kinds of users. But does this VPN live up to give the actual value for money that it claims? Surfshark also offers thousands of servers worldwide, excellent…
-

ProtonVPN
ProtonVPN is a virtual private network (VPN) service provided by Proton Technologies AG, the company behind the email service ProtonMail. ProtonVPN was created to provide a secure, private, and censorship-free internet connection to people all over the world. It encrypts your internet connection and hides your IP address, making it difficult for hackers, ISPs, and…
-

NordVPN
NordVPN is a Virtual Private Network (VPN) service provider that was founded in 2012 by four childhood friends in Panama. The company is now headquartered in Cyprus, with offices in the United States, the United Kingdom, and Lithuania. NordVPN is one of the most well-known VPNs in the market, and this is due to their…