Tag: 31173
-

Mullvad
Mullvad is a small but mighty VPN provider that offers incredible speeds along with security and performance that stacks up with the best VPNs. Mullvad VPN is fast, great for torrenting, and excellent at keeping you safe online. It uses AES-256 encryption, OpenVPN and WireGuard protocols, multi-hop, and a dependable kill switch. However, Mullvad prioritizes…
-

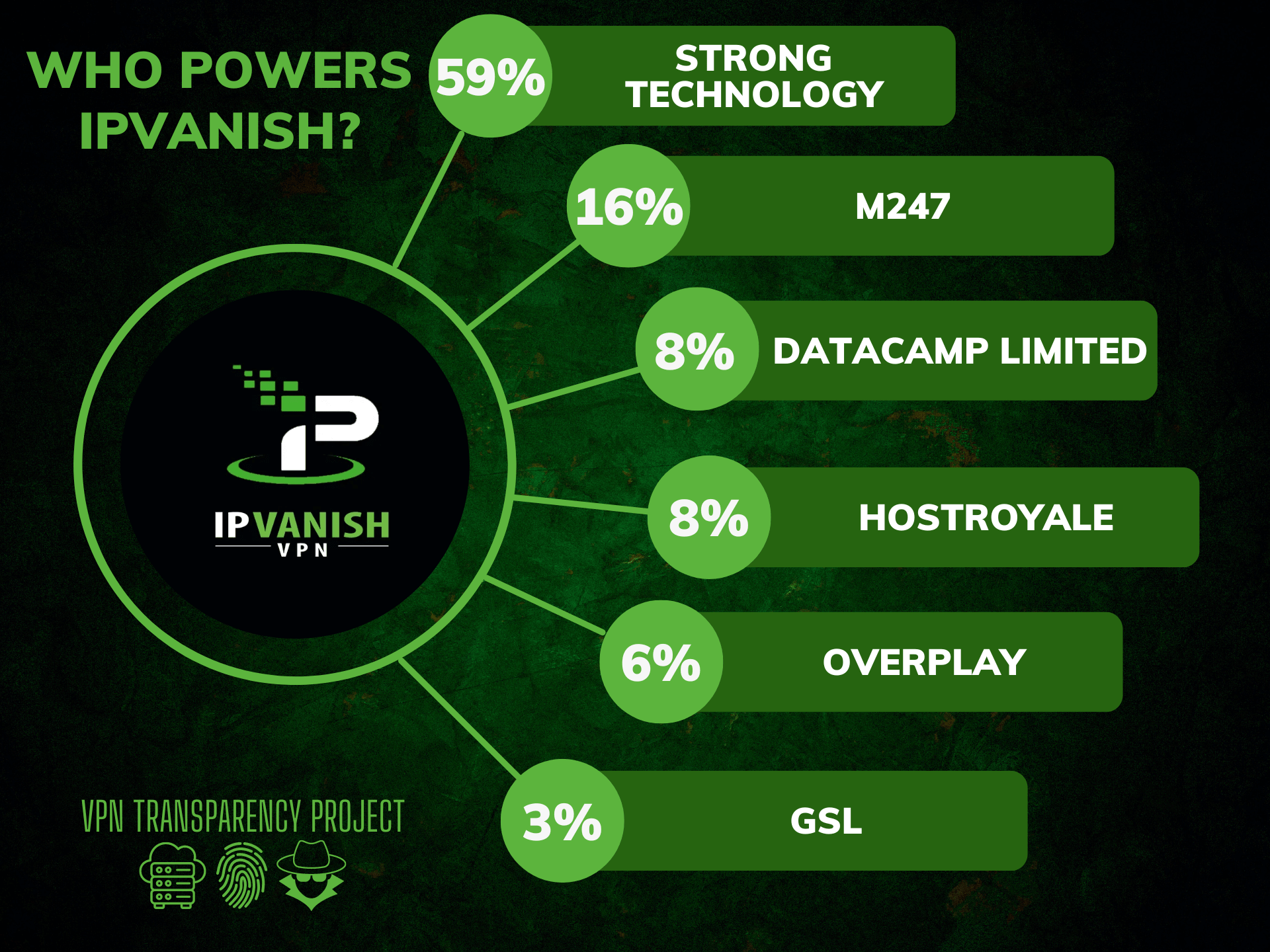
IPVanish
IPVanish is a virtual private network (VPN) service that allows users to securely and anonymously access the internet. A VPN creates a secure, encrypted connection between a device and the internet, protecting data and preventing snooping or tampering by third parties. IPVanish offers a range of VPN products and services, including support for Windows, Mac,…
-

Windscribe
Windscribe, a cross-platform virtual private network (VPN) service provider, was founded by Yegor Sak and Alex Paguis in 2016. Based in Canada, it has grown to operate internationally, supporting a broad range of operating systems and platforms, and providing services to personal computers, smartphones, routers, and smart TVs1. The company’s offerings include OpenVPN, Internet Key…
-

Surfshark
Surfshark VPN is one of the most popular VPN services in 2022. Its competitive price and unlimited simultaneous connections make it a very attractive VPN option for all kinds of users. But does this VPN live up to give the actual value for money that it claims? Surfshark also offers thousands of servers worldwide, excellent…
-

CyberGhost VPN
CyberGhost VPN was founded in 2011 in Bucharest, Romania, and initially began as a free VPN service. By the following year, it had gathered around 1.7 million users. In 2017, a notable change occurred when Kape Technologies (then known as Crossrider) acquired CyberGhost VPN. This acquisition brought about concerns among observers due to Crossrider’s background…
-

Aloha Browser VPN
The Aloha Browser is one of the up-and-coming new browser apps for mobiles which targets one of the most important aspects of modern browsing — privacy. The Aloha Browser is the only browser (to our knowledge) that comes with a built-in VPN and encrypts user data at all levels. When you are using Aloha VPN…
-

Mozilla VPN
When you are using Mozilla VPN, whose servers are you really using? According to my research, Mozilla leases hardware from a few different well known providers such as Datacamp Limited, Tzulo, 31173 Services, and xTom. Some people are drawn towards Mozilla VPN because they are already familiar with Mozilla’s Firefox browser and so the name…
-

Private Internet Access
Table of Contents Privacy Policy Terms of Service Log Policy Torrenting Use of virtual servers ASN Diversity Private Internet Access (commonly known as PIA) is a capable VPN provider, now owned by Kape, which also owns CyberGhost, ZenMate and ExpressVPN. PIA has servers available in just about every single state in America, which is great…